Overview: What Is Dirty Frag
Just when the Linux community was recovering from the “Copy Fail” exploit, a new and potentially more dangerous zero-day has emerged: Dirty Frag. Disclosed on May 7, 2026, this Universal Linux Local Privilege Escalation (LPE) vulnerability allows any unprivileged user to gain full root access in seconds.
At Limitless Hosting, we understand that in the world of web hosting, minutes matter. That is why our security team has already deployed patches and mitigations across our managed infrastructure. If you are running your own unmanaged servers, this guide is your essential roadmap to securing your data immediately.
What is the Dirty Frag Vulnerability?
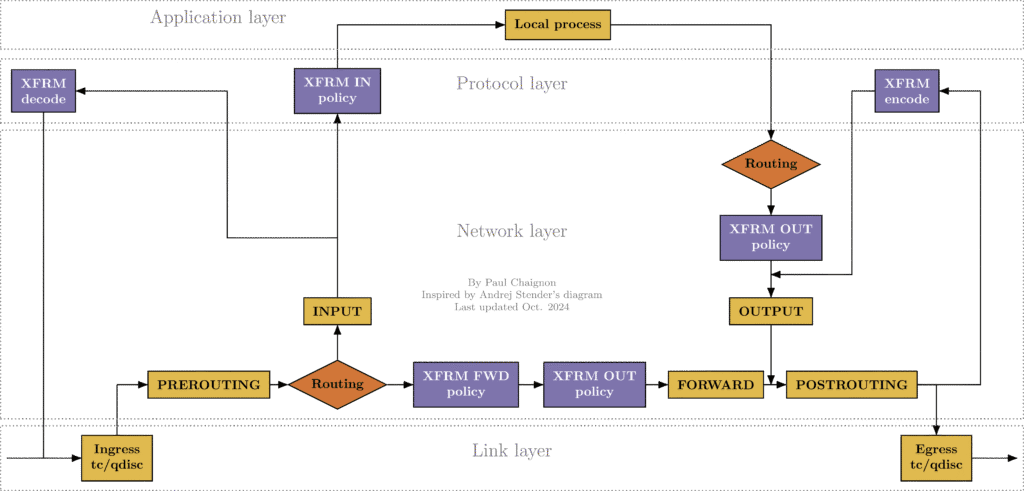
Dirty Frag is a critical logic flaw residing in the Linux kernel’s xfrm (IPsec) and rxrpc subsystems. The vulnerability specifically targets the MSG_SPLICE_PAGES code path used for ESP-in-UDP processing.
Technically, it is a “no-COW” (Copy-on-Write) error. Normally, the kernel ensures that if a user tries to modify a page of memory that is shared, a private copy is made first. Dirty Frag bypasses this protection, allowing an attacker to write directly into the kernel’s page cache.
This means an attacker can tamper with sensitive system files—like /etc/passwd or /usr/bin/su—while they are stored in memory, effectively granting them instant root privileges. If not detected early, it can cause serious problems, that’s why continuous domain monitoring is important.
Key Details of the Exploit:
- Vulnerability Name: Dirty Frag (Local Privilege Escalation)
- CVE Status: Pending (Disclosure occurred before official coordination)
- Affected Subsystems: xfrm (IPsec) and rxrpc
- Impact: Immediate Root Access for local users
- Complexity: Low; a public Proof-of-Concept (PoC) is already circulating on GitHub.
Why Dirty Frag is a “Universal” Threat
Unlike some vulnerabilities that only affect specific configurations, Dirty Frag is “universal” because the xfrm netlink interface is accessible to unprivileged users on almost every major Linux distribution. Even if you don’t actively use IPsec or VPNs, the kernel may auto-load the vulnerable modules (esp4 and esp6) the moment an exploit script calls them.
This follows the pattern of the recent Copy Fail (CVE-2026-31431) vulnerability but strikes a different part of the kernel, making it a “double-whammy” for system administrators who haven’t updated their kernels in the last week.
Are You Vulnerable? Affected Distributions
Dirty Frag affects almost all modern Linux kernels (typically versions 5.x, 6.x, and the new 7.x branch). This includes:
- Ubuntu 22.04, 24.04, and 26.04 LTS
- Debian 11, 12, and 13
- AlmaLinux 8, 9, and 10
- CloudLinux 7h, 8, 9, and 10
- CentOS Stream and RHEL
Blazing Fast VPS Hosting.
Get the speed your website deserves with storage and optimized server resources.
How to Fix Dirty Frag: The Ultimate Guide
There are two ways to handle this: the Permanent Fix (reboot) and the Immediate Mitigation (no reboot required). At Limitless Hosting, we have already handled this for our managed clients, but here is how you can do it yourself.
Method 1: The Permanent Fix (Update and Reboot)
Major distributions are releasing emergency kernel updates. You should update your system packages and reboot as soon as possible.
| OS Family | Command |
|---|---|
| Ubuntu / Debian | sudo apt update && sudo apt upgrade -y && sudo reboot |
| AlmaLinux / RHEL / CentOS | sudo dnf update -y && sudo reboot |
Method 2: The 30-Second Mitigation (No Reboot)
If you cannot afford a reboot right now, you can “neutralize” the attack surface by preventing the vulnerable modules from loading. This is the same technique used by security researchers to stop the exploit cold.
Warning: This will break IPsec-based VPNs (like strongSwan or Libreswan). It does not affect WireGuard, Tailscale, or OpenVPN.
- Blacklist and unload the modules:
Run this command to prevent the esp4, esp6, and rxrpc modules from being loaded and to remove them if they are currently active
sudo sh -c "printf 'install esp4 /bin/false\ninstall esp6 /bin/false\ninstall rxrpc /bin/false\n' > /etc/modprobe.d/dirtyfrag.conf; rmmod esp4 esp6 rxrpc 2>/dev/null; true"- Clear the Page Cache (Critical Step):
Because this vulnerability allows an attacker to alter system binaries directly within the page-cache to gain root access, simply blocking the modules is insufficient if the system was already compromised. You must force the kernel to drop the page-cache to ensure no malicious modifications remain in memory.
sudo sh -c "echo 3 > /proc/sys/vm/drop_caches"- Reverting the Mitigation:
To revert these changes: Once you have successfully installed a patched kernel and rebooted, you can restore the modules by removing the configuration file:
sudo rm /etc/modprobe.d/dirtyfrag.confLimitless Hosting: Secure, Managed, and Ahead of the Curve
In the hosting industry, speed is often marketed as “faster CPU” or “NVMe drives.” But at Limitless Hosting, we believe speed also applies to Security Response & Dealing with Cybersecurity Threats.
While many providers are still “investigating” the Dirty Frag impact, our managed server clients are already protected. We don’t just provide space; we provide peace of mind. By choosing Limitless Hosting, you get:
- Zero-Day Response: We monitor security channels (like oss-security) 24/7 to apply mitigations before exploits go mainstream.
- Automated Patching: Our systems utilize live-patching technologies where possible to fix kernel bugs without downtime.
- Expert Support: Not sure if your custom kernel is vulnerable? Our experts are here to check it for you.
Don’t wait for a “Rooted” notification to arrive in your inbox. Move your workloads to a provider that takes security as seriously as you do.
Dirty Frag FAQ
Does Dirty Frag affect Docker or LXC?
Yes. Because containers share the host’s kernel, a “Dirty Frag” exploit run inside a container can potentially compromise the entire host system.
Is this the same as Dirty Pipe?
It is in the same family. Like Dirty Pipe and Copy Fail, it exploits the kernel’s memory management (page cache), but it uses the xfrm subsystem as the entry point.
Will my website go down if I apply the fix?
Standard web hosting workloads (Apache, Nginx, MySQL) do not use esp4 or esp6. Applying the mitigation (Method 2) is safe for 99% of web servers.
Stay safe, keep your kernels updated, and remember: The best defense is a proactive host.
Read our latest posts:
- How to Host a Website in cPanel: The Beginner’s Guide to Launching Your Site
- Reseller Hosting vs VPS: The Ultimate Web Agency and Developer Decision Guide
- How Is AI Impacting the Web Hosting
- The Need for Speed: Importance of Fast Website Loading Speed
- How Much Does a Blesta License Cost? The Complete 2026 Pricing Blueprint